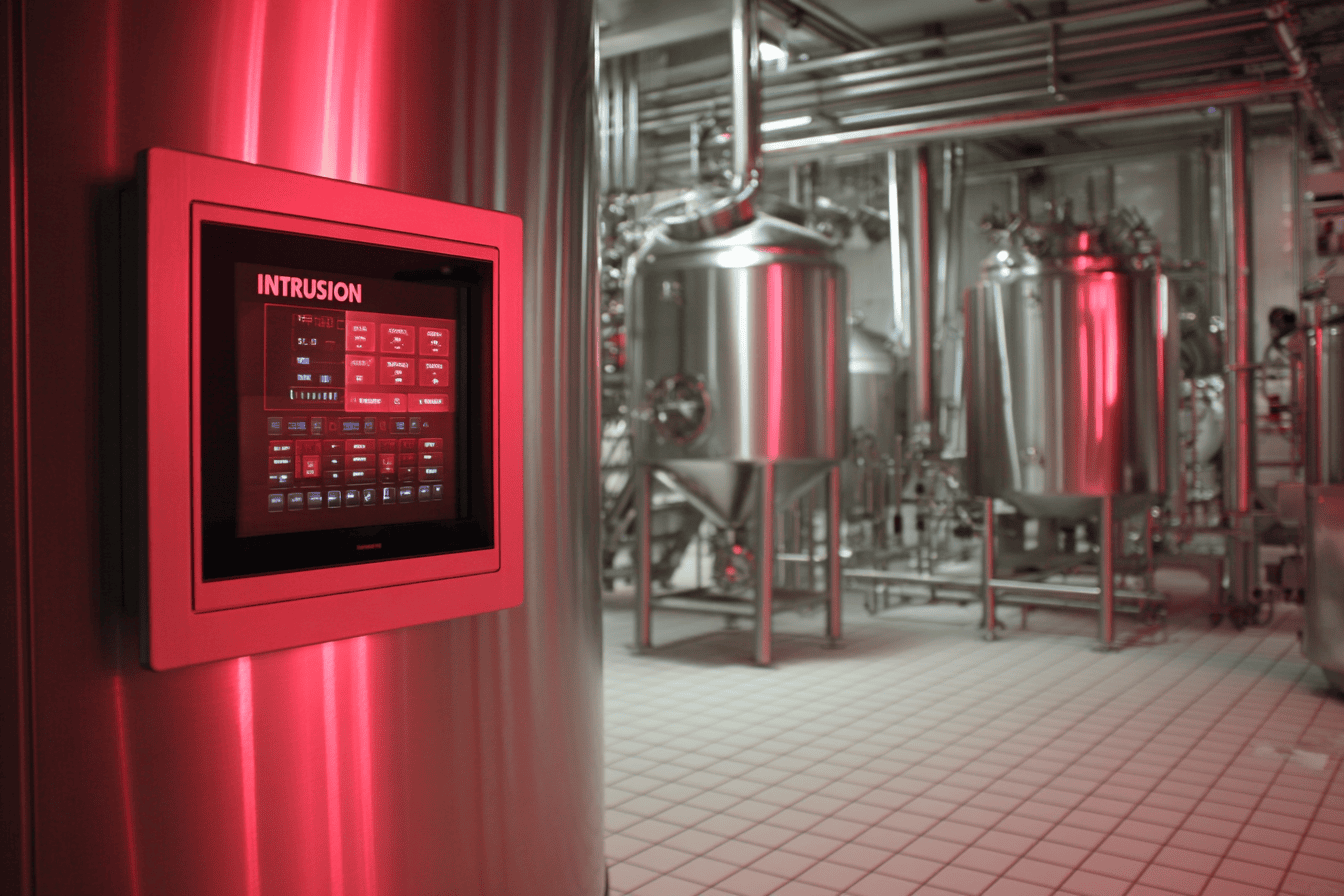
Global manufacturers run highly connected operations where information technology (IT) and operational technology (OT) are tightly intertwined. When a network is breached, the fallout is rarely contained to just office computers. Disrupted systems cause production to stall, shipments to slip, and downstream customers to feel the impact immediately.
Mid-sized plants face the exact same pattern on a smaller scale. One cyber incident can put your production lines, customers, and cash flow at risk. This post explains the realities of OT cyber risk for manufacturing companies and provides practical steps to keep your operations running safely.
The High Cost of Disrupted Operations
Large-scale breaches provide a clear warning for businesses of all sizes. In 2021, automotive supplier Yazaki faced a ransomware incident in which attackers stole sensitive data from the company. This event highlighted how vulnerable complex, globally distributed manufacturing environments can be.
That same year, ransomware hit JBS Foods, one of the world’s largest meat processors. The company had to shut down multiple plants for several days and ultimately paid a large ransom to restore operations.
In 2023, Dole reported a cyberattack that disrupted its North American operations. The company temporarily shut down some production, which contributed to shortages of packaged salads on U.S. store shelves.
These incidents show that a single breach can halt production, create supply chain chaos, damage customer trust, and erase profit across regions.
A Simple Example for Mid-Sized Plants
A mid-sized components manufacturer supplying assemblies or harnesses to automotive and other industrial customers might not be a household name. However, it often plays a critical role in someone else’s just‑in‑time supply chain.
If ransomware enters via IT and forces OT systems offline, that plant experiences the same dynamics Yazaki, Dole, and JBS do. Systems might go offline to contain the attack, or they might fail because shared infrastructure is affected. Either way, the lines stop. Customers cannot be served, and leadership must navigate high‑pressure decisions about downtime, recovery, and reputational impact.
How to Protect Your Plant
You don't need an experienced, full-time CTO to make your security better than it is right now. Start with these actionable steps:
- Maintain a current inventory: Keep an updated list of both IT and OT assets. You must know what equipment and software you have so you know what you are actually protecting.
- Segment OT from IT: Build a digital wall between your networks. This setup ensures that an office‑side incident cannot easily cascade into your production lines.
- Tighten and monitor remote access: Limit what stolen credentials can reach. Pay close attention to the access you grant to third-party vendors and integrators.
- Run tabletop exercises: Prepare your leadership team. Executives and plant managers should know exactly how they will respond before a real incident hits.
Secure Your Production Lines Today
If your business can't afford a Yazaki‑, Dole‑, or JBS‑style disruption, now is the time to stress‑test your OT security posture.
Click the "Let's Talk" button below or call 913-624-1675 to learn how a focused OT/IT risk review for manufacturers can identify your most critical exposures. Implement practical, scalable steps to reduce the chance that a cyber incident stops your lines. You can unlock your business potential and drive growth confidently by ensuring your technology is resilient. Reach out today to schedule your review.